Introduction to ADAS- Advanced Driving Assistance System
ADAS system is considered as the advancement from driver
assistant system (DAS). DAS is a system that informs and warns, provides
feedback on actions, increases comfort, and reduces workload by actively stabilizing
or maneuvering the vehicle. ADAS system is considered as a subset of DASs, with
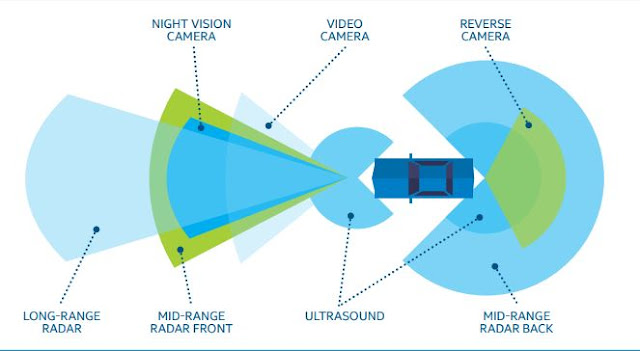
increased use of complex processing algorithms to detect and evaluate the
vehicle environment based on data collected via a variety of sensor inputs. The
ADAS usage cases that require full power of real-time processing and
intelligence are highlighted with full stars, whereas half-colored star marked
usage cases are relatively more rudimentary ADAS cases.
There are several challenges to design, implement, deploy, and operate ADAS. The system is expected to gather accurate input, be fast in processing data, accurately predict context, and react in real time. And it is required to be robust, reliable, and have low error rates. There has been significant amount of effort and research in the industry to solve all these challenges and to develop the technology that will make ADAS and autonomous driving a reality. In addition to functional requirements, ADAS must be secured from adversaries with malicious intent whose goal is to compromise the system and cause catastrophic accidents with loss of life and damage to property. It has been shown both in academia and automotive industry that control system can be compromised via malicious attacks launched through various means, for example via DVD player, the ODB-II port,1,2 or even wirelessly via tire pressure sensors,3 as a result displaying to the driver wrong warnings3 or even causing fatality by remotely disabling braking system on a vehicle while it is moving.1,2 In addition to protecting the system from criminal actors, there is a bigger threat looming from nation-state sponsored cyber terrorism. In this whitepaper we argue that ADAS security should be considered as a fundamental non-functional requirement— together with reliability, robustness, performance, and low error rates. We analyze vulnerabilities in a conceptual ADAS architecture via representative use cases. Based on the vulnerability analysis results we state security requirements and make suggestions on countermeasures against malicious attacks. We show that ignoring ADAS security compromises other design goals.
Comments
Post a Comment